nCuX (Роман Селезнев) - non-public материалы дела
Автор: sp0raw (http://sporaw.livejournal.com/466632.html)
(Документы чуточку эксклюзивны)
Из которых мы узнаем, что...
... года с 2009 (минимум) его уже были готовы принять:
1) Federal agents eventually developed evidence that Roman Seleznev, the son of a Russian politician, was the true identity behind nCuX. On May 19, 2009, agents with the Secret Service and the FBI met with representatives of the Russian Federal Security Service (FSB) in Moscow, and presented substantial evidence of defendant’s computer hacking activities including his credit card hacking and other computer crimes. U.S. law enforcement provided the FSB with defendant’s online alias names and information that they believed nCuX’s true name was Roman Seleznev of Vladivostok, Russia. The agents’ attempt at international coordination backfired. Just one month later, on June 21, 2009, nCuX notified his co-conspirators on multiple criminal forums that he was going out of business. Shortly after that, nCuX completely disappeared from the Internet.
... года с 2008 (минимум) он был информатором ЦИБ ФСБ:
2) As U.S. Probation noted, the information that U.S. law enforcement was investigating Seleznev “clearly got back to Mr. Seleznev.” Indeed, Seleznev had his own contacts inside the FSB. In chat messages between Seleznev and an associate from 2008, Seleznev stated that he had obtained protection through the law enforcement contacts in the computer crime squad of the FSB. Later, in 2010, Seleznev told another associate that the FSB knew his identity and was working with the FBI.
//
As U.S. Probation has noted, Seleznev had multiple opportunities to reassess his life and end his career as a hacker. The first was when U.S. law enforcement agents went to Russia and met with Russian law enforcement regarding Seleznev’s activities as nCuX. Despite acknowledging to his co-conspirators that he had been tipped off by the FSB, Seleznev merely abandoned his original alias and began building new criminal infrastructure under new alias names of Track2 and Bulba.
//
Additionally, in light of his history of contacts with Russian law enforcement, he is likely to act with impunity upon return to Russia. Because he cannot be extradited from Russia and will likely be even more careful in his travels than before, if he returns to his criminal enterprise, he will forever remain beyond the reach of U.S. law enforcement.
... с деньгами у него было все более, чем хорошо (~$18M только LR, а были еще WM, BTC, WU и др.):
3) Seleznev made tens of millions of dollars through his fraud. He collected payments via online payment systems including Bitcoin, Liberty Reserve and WebMoney. Because these payment systems were designed to protect user anonymity, law enforcement will never know how much money Seleznev collected in total. However, one of these payment systems—Liberty Reserve—was seized by the government in connection with another criminal investigation. Liberty Reserve records show that Seleznev collected approximately $17 million in sales in approximately three years, 2010 – 2013, through this one payment system alone. Seleznev undoubtedly collected many millions more using Bitcoin and other currencies throughout his lengthy criminal career.
Seleznev used this money to live an extravagant lifestyle. He purchased two properties in Bali, Indonesia and jetted between Bali and Vladivostok at will. Photographs on Seleznev’s phone show his associates with large bundles of cash, at luxurious resorts, and posing for photographs next to high-end muscle cars. Immediately before his capture, Seleznev spent over $20,000 to stay in a resort in the Maldives, boasting to an associate in a chat that “I took the most expansive villa” and that “I have my own manservant.”
//
The property to be forfeited included a money judgement representing the proceeds Seleznev obtained as a result of the offenses charged in the Second Superseding Indictment. The evidence at trial established that Seleznev received $17,886,971.09 in proceeds from the sales of stolen credit card data through Liberty Reserve. See Trial Exhibit 9.11; Tr. 725-726. This amount surely understates Seleznev’s total earnings from this scheme as it only captures one of several payment mechanisms he used over the course of the scheme. Nonetheless, it provides the most direct evidence of the proceeds defendant obtained as a result of his hacking scheme. Therefore, the government is seeking a money judgment in the amount of $17,886,971.09.
//
These records as outlined above, establish that defendant obtained $17,886,971.09 through Liberty Reserve alone. Therefore, this figure represents a very conservative money judgment in light of the fact that defendant also used Web Money, Western Union and other payment channels to receive payments from his customers.
... мониторил pacer на предмет своих имен/данных, а в ответ мониторили его (и не летал туда, где считал, что США имеют возможности):
4) The grand jury charged Seleznev in a sealed indictment on March 3, 2011. Seleznev remained at large for over three years. During this period, Seleznev carefully evaded apprehension, employing practices like buying last-minute plane tickets to avoid giving authorities advance notice of his travel plans. Seleznev obtained an account with the U.S. Court’s PACER system, which he monitored for criminal indictments naming him or his nicknames. He avoided travel to countries that had entered into extradition treaties with the United States. Indeed, when Seleznev was finally confronted by U.S. agents in the Maldives, his first words were to question whether the United States had an extradition treaty with the Maldives. Tr. 231.
... как непосредственно сработали США:
5) The circumstances of Seleznev’s capture demonstrate the extreme difficulty of apprehending foreign cybercriminals. On July 1, 2014, the United States received information that Seleznev was vacationing in the Maldives, and would be departing from that country on July 5, 2014. This provided agents four days to (1) seek internal U.S. government clearances to conduct a foreign operation; (2) obtain agreement from the Maldives to turn Seleznev over without a formal extradition treaty; (3) mobilize Secret Service agents to the Maldives (an 18-hour flight from Hawaii); (4) coordinate the logistics of the apprehension with the local authorities; (5) arrange for private transportation (a private jet sufficient range to fly many thousands of miles over water) to take Seleznev to the nearest U.S. territory; and (6) take custody of Seleznev.
As a result of extraordinary efforts by the Secret Service, the Departments of Justice and State, and Maldivian authorities, the government was able to clear these hurdles, and took Seleznev into custody on July 5, 2015. However, in imposing sentence, the Court should consider the near-impossibility of apprehending Seleznev again if he returns to crime after his release.
... немного про отца и противодействие правосудию:
6) Seleznev repeatedly attempted to manipulate and protract these proceedings, resulting in a cumulative delay of 26 months, and six sets of counsel, between his capture and trial. For example, the Court will recall that the evidentiary hearing on Seleznev’s motion to dismiss was originally set for May 13, 2015. Transcripts of jail calls previously submitted to the Court reveal that, in the days leading up to the hearing, Seleznev and his father resolved to delay the hearing so that they could work on a secret strategy they elliptically referred to as “Uncle Andrey’s option.” To manufacture the delay, Seleznev’s father suggested that Seleznev either “get sick” or “completely stop the communication with the lawyers.”
//
Once in the Western District of Washington, he spent nearly three years burning through attorney after attorney. While he now claims he only went to trial based on the bad advice of his attorneys, recorded calls from the FDC between defendant and his father demonstrate his attorneys repeatedly encouraged him to negotiate a plea agreement, and each time he was given this advice, he became frustrated with counsel, insisted on going to trial, and ultimately fired each successive set of attorneys. Although he now freely admits he is guilty, he pursued motions to suppress evidence based on misleading arguments that the government or some unknown super hacker had planted evidence on his computer.
... его сильно грабанули в 2009 году по наводке (это к вопросу всяких друзей-корешей, которые знают вас и ваше состояние):
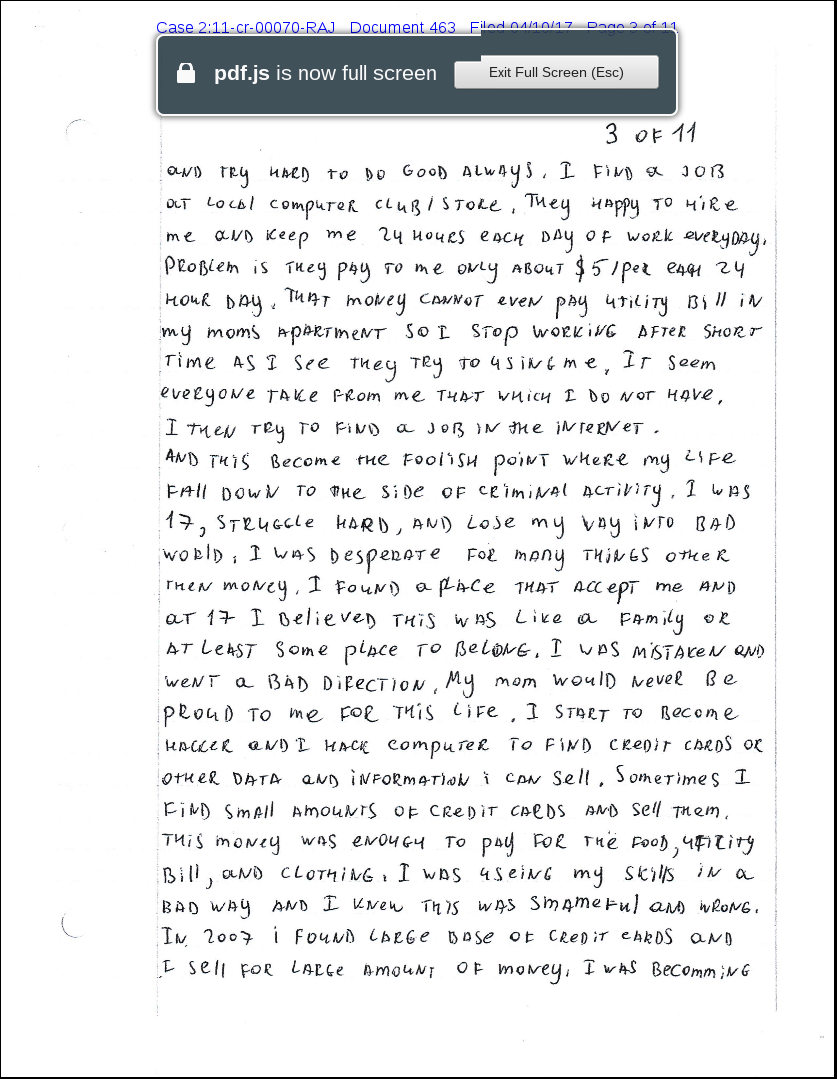
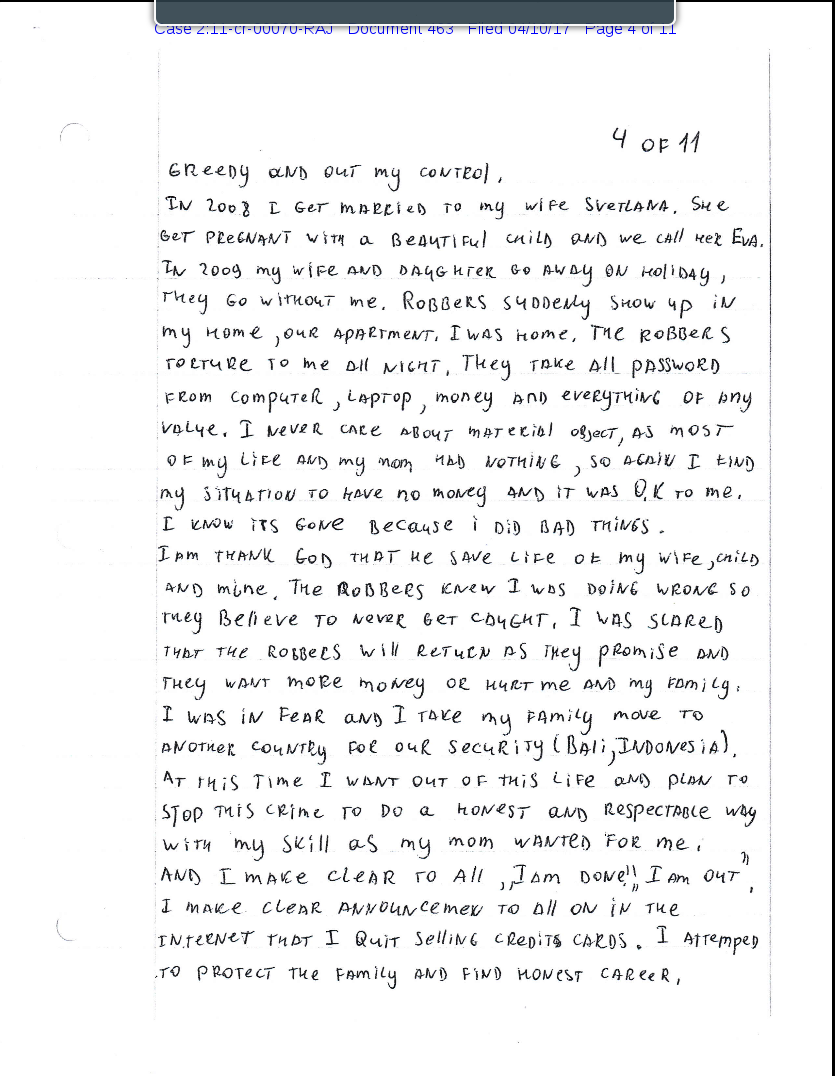
7) In 2009 robbers broke into his apartment and tortured him all night to force him to reveal location of his money. To protect his family Mr. Seleznev temporarily moved to Bali, Indonesia. In Bali Mr. Seleznev quit all criminal activity, and on the Internet announced to his associates that “I am done. I am out from selling stolen credit cards.” Unfortunately, at that time, he was not strong enough to keep that promise.
... пошел (пытался пойти) на сотрудничество в максимально возможном объеме
8) Moreover, he wants to actively rectify the consequences of his criminal actions and to use his knowledge and experience to prevent new cyber-attacks perpetrated by others. With that in mind, there has been ongoing discussion with the government to determine the best way he can assist in fighting cybercrime. Mr. Seleznev has made significant and proactive efforts to establish cooperation with the government. Over the past few months Mr. Seleznev has handed over to the government four laptops and six flash drives. In addition, he participated in a two-day proffer session. Most importantly, regardless of the sentence he receives, Mr. Seleznev is ready at any time to use his experience and skills in helping the government stopping cybercrime.
... не сотрудничал длительное время, при том, что в таких делах ценится именно время (чем позже решил сотрудничать - тем меньше ценность этого сотрудничества):
9) As the Court is already aware, Seleznev first met with the government in December 2014, purportedly to provide assistance to the government. At that time, shortly after defendant’s arrest, the information he possessed may have been helpful in furthering other government investigations. In advance of the meeting, the government repeatedly told defense counsel that the value of any information defendant might have was extremely time-sensitive given the dynamic nature of the carding industry. The government made clear that the value of cooperation would be diminished or non-existent if Seleznev waited until after the trial, which was then set for May 4, 2015.
Defendant, nonetheless, chose not to cooperate. While he met with the government in December 2014, defendant was combative and repeatedly refused to identify others he had conspired with or those he knew were involved in criminal behavior. When asked why he would not name others or provide information regarding others involved in cybercrime, defendant explained that he was withholding that information as bargaining chips. When told that the government would require a complete statement from defendant before negotiating the terms of a cooperation agreement, defendant terminated the proffer session stating that he thought the proffer was supposed to be a “negotiation.” Defendant provided no information of value to apprehending other targets.
During the 20 months between the first “proffer” session and the eventual trial, the government and defense counsel had many discussions about the possibility of cooperation. The government repeatedly advised the defense that time was of the essence, and that defendant had already seriously compromised the value of his information by refusing to cooperate in the months following his apprehension. Defendant provided no additional information to the government over this 20-month period.
//
Defendant’s belated effort to cooperate is insufficient to justify any reduction in his sentence. For law enforcement to make effective use of assistance in cybercrime investigations, they need timely and complete information from a cooperating defendant. The time to cooperate is in the immediate days and weeks after they are arrested. As time passes, the value of any information a cybercriminal may possess quickly dissipates as co-conspirators learn about the potential cooperator’s arrest, change their online identities, and move to new infrastructure. Defendant was fully aware of the fact that time was of the essence if he were to be useful to government. If he had provided useful information when he first met with the government in 2014, this case may have turned out very differently. Defendant, however, made a choice to throw that opportunity away and proceed to trial. In light of his explicit refusal to provide useful information when it was most valuable, he should not be rewarded for his belated efforts to cooperate.
... отказали в сотрудничестве, потому что всю необходимую информацию имеют уже и так:
10) Following his conviction at trial (over two years after his apprehension), defendant again requested an opportunity to meet with the government and provide information. Although defendant’s potential usefulness has declined substantially as a result of the passage of time, the government agreed to meet with defendant and participated in proffer sessions on March 28-29, 2017. Unfortunately, he did not have any particularly useful information. Defendant acknowledged his guilt and that of his co-conspirators on the carding forums. He also identified some of those he conspired with between approximately 2005 and his capture in 2014. Much of the information that he provided, however, was already well known to the Secret Service. Defendant simply did not have any immediately actionable information that could assist law enforcement. As such, the information he provided was mainly useful as background intelligence. Furthermore, Seleznev made statements that the government believes to be demonstrably false, thereby further undermining the value of any information he provided.
Оригиналы документов:
- DEFENDANT’S MOTION TO SEAL - NOTE ON MOTION CALENDAR: April 14, 2017
- SENTENCING MEMORANDUM (наиболее интересный документ)
- Victim Restitution Amounts per Victim Financial Loss Restitution Statements
- UNITED STATES’ NOTICE OF FILING PAPER MATERIALS WITH THE CLERK
- SENTENCING MEMORANDUM (тоже)
- WOOD - Cross (by Ms. Scanlan)
- Letter: King of Morocco
- DISCHARGE SUMMARY FROM HISTORY OF DISEASE CASE No. 2635 (мед документы: перевод; часть дела)
- Bureau of Prisons - Health Services - Clinical Encounter
- DISCHARGE SUMMARY - History of the disease 1106 (мед документы - перевод; часть дела)
- REPORT OF INSPECTION BY GASTROENTEROLOGIST-HEPATOLOGIST (мед документы - перевод; часть дела)
- SUPPLEMENTAL SENTENCING MEMORANDUM (интересно - сотрудничество невозможно, все известно)
- STATEMENT FORM
- FDC PHONE TRANSLATIONS (переводы разговоров по телефону)
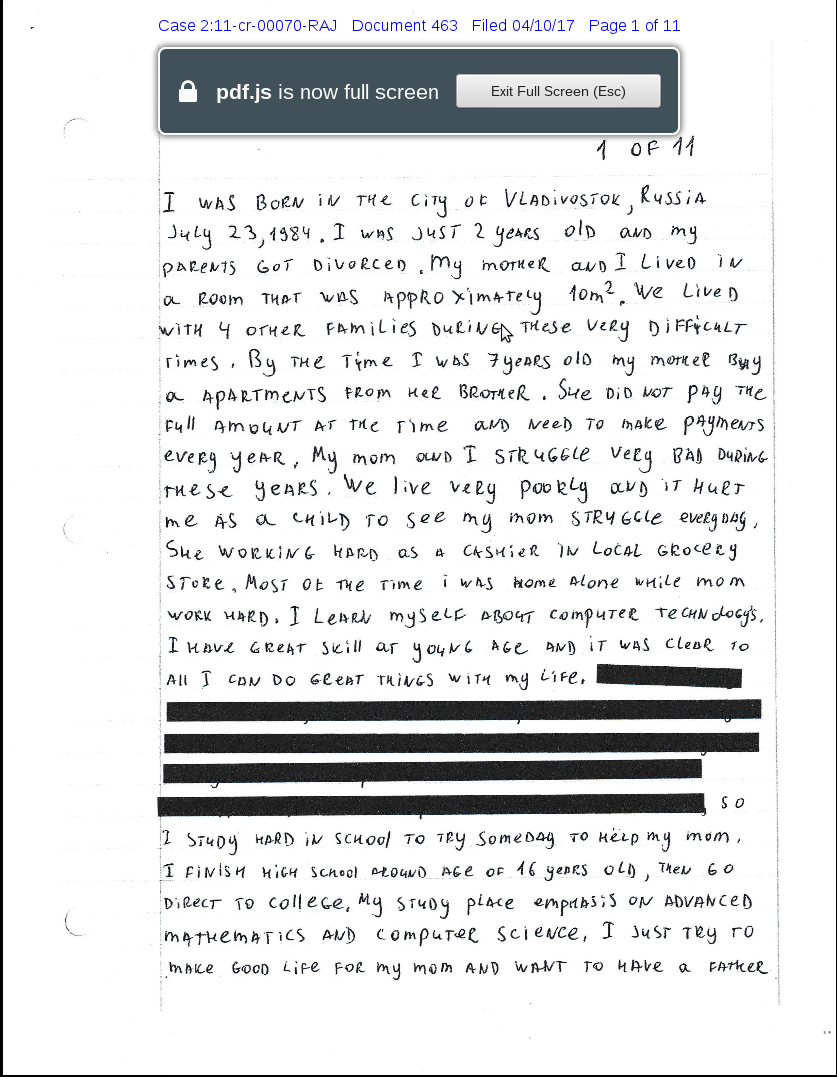
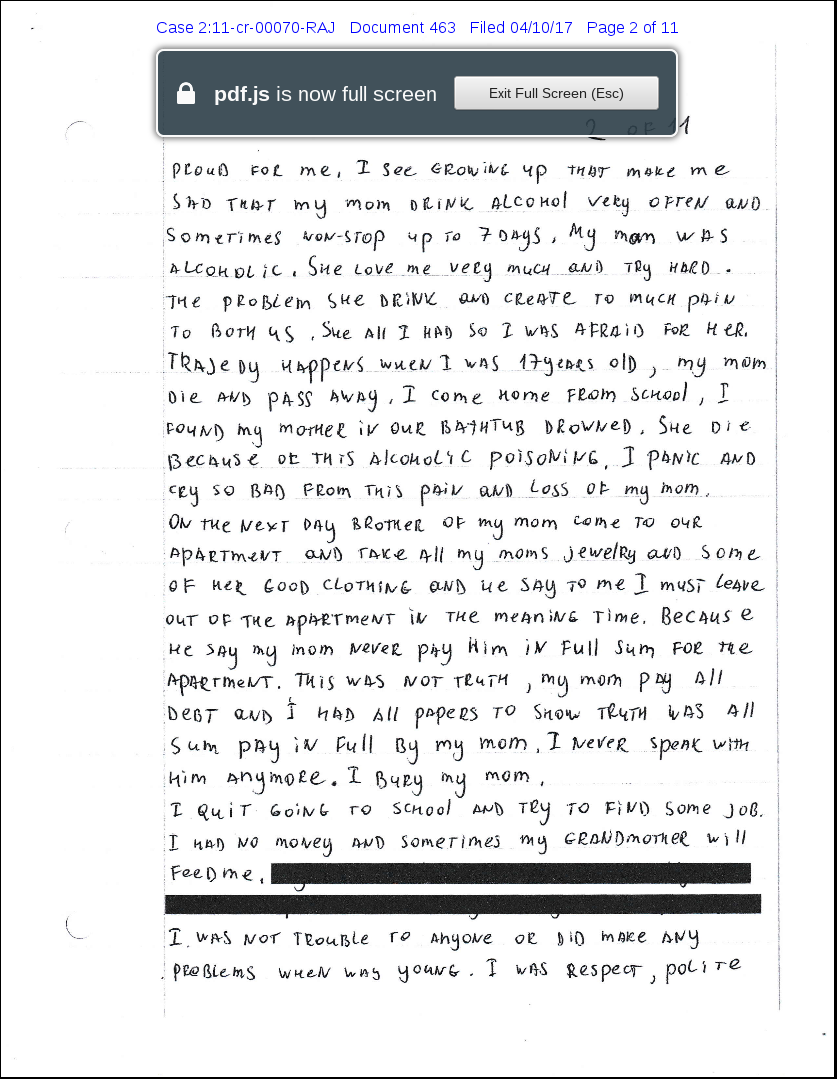
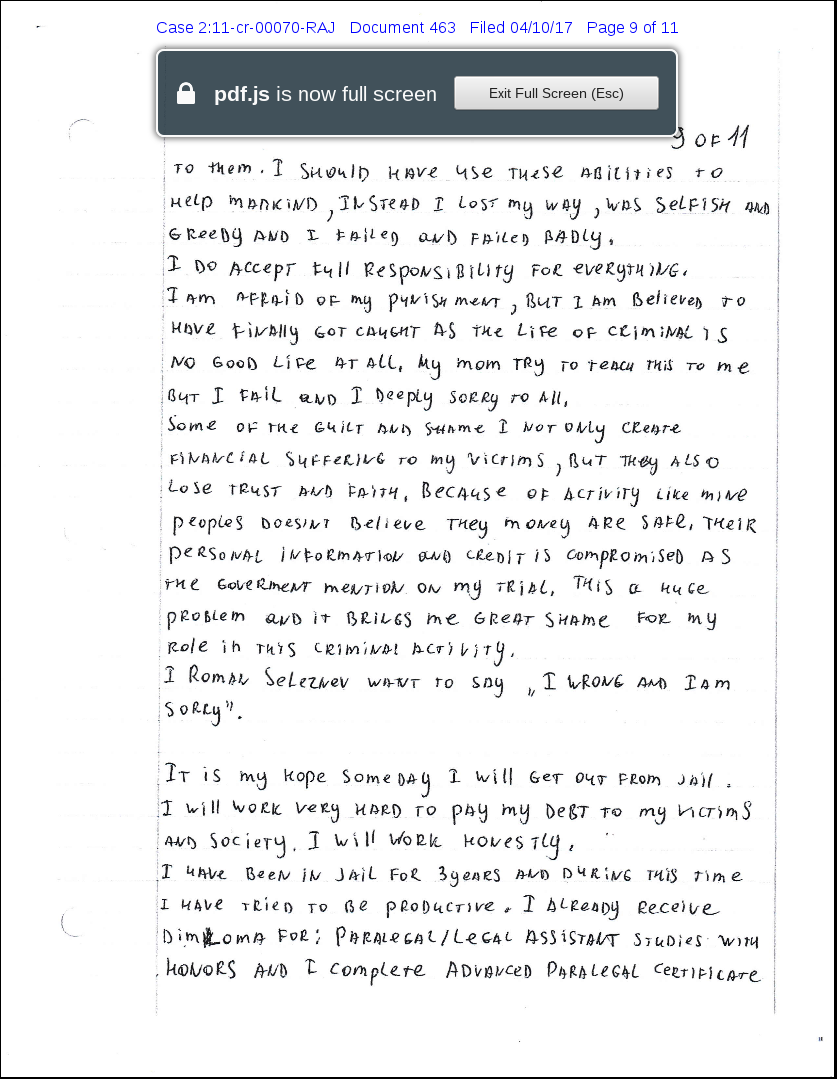
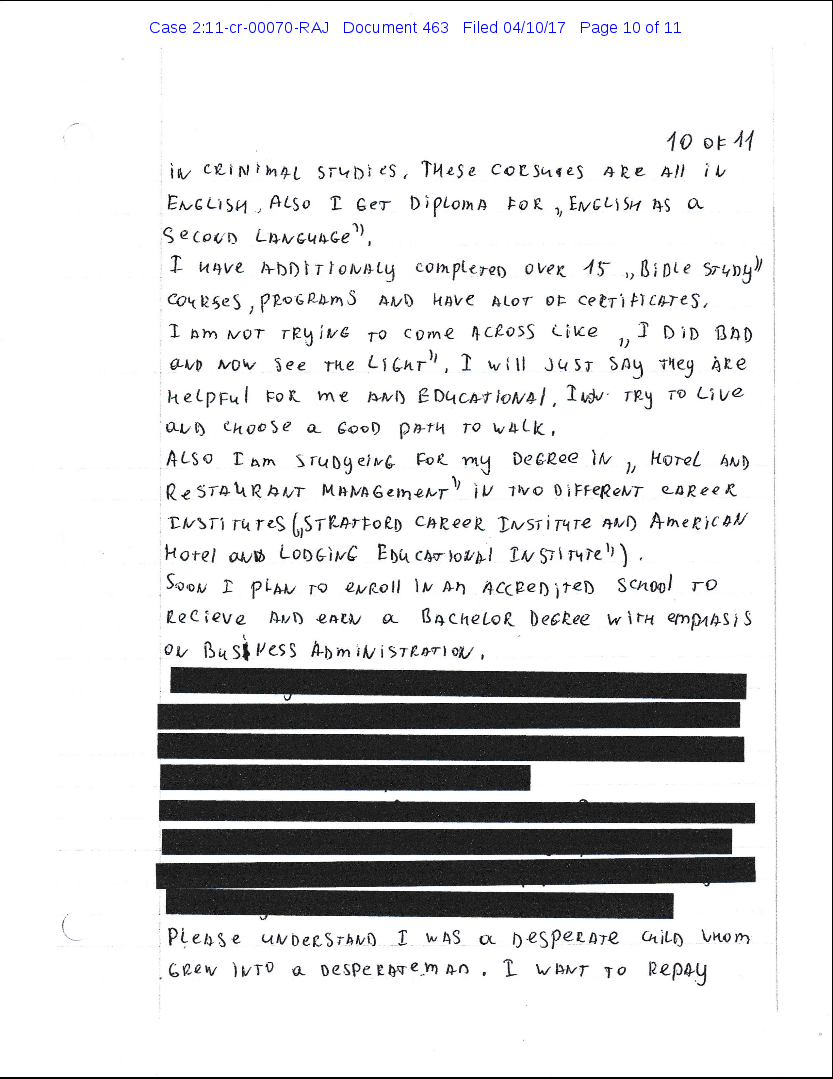
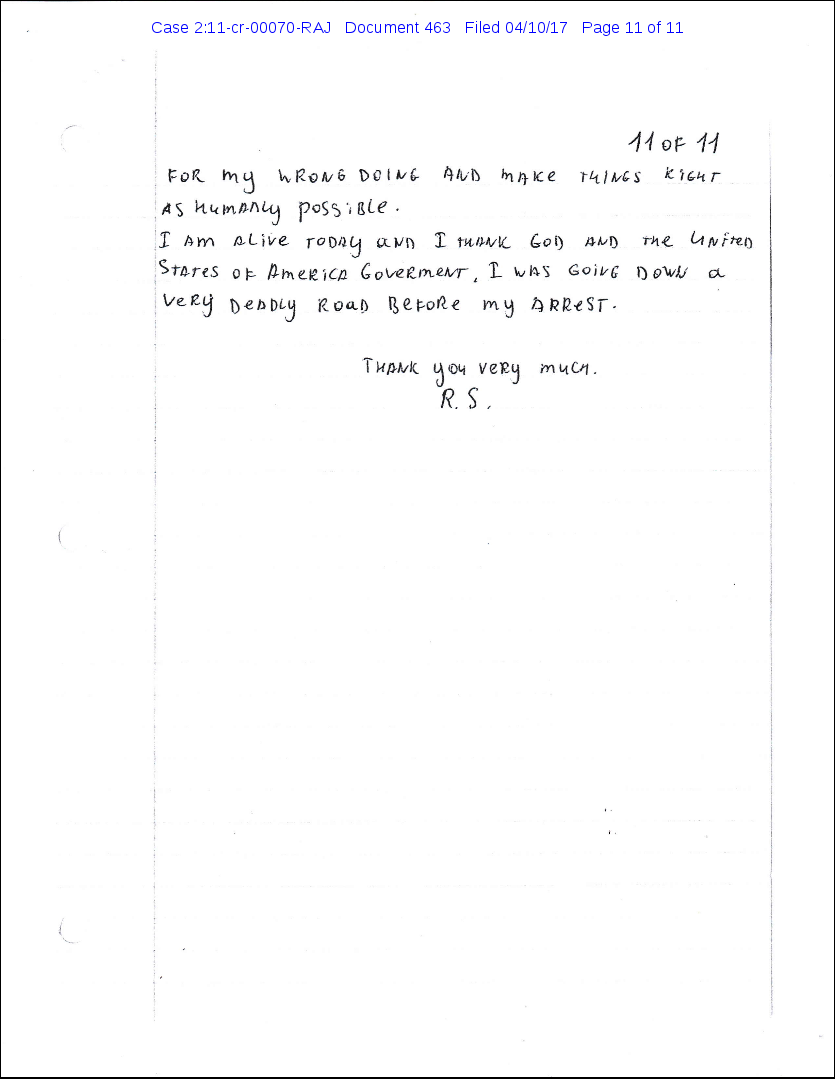
"Признание" для суда (19717408018.pdf) (прошу прощения за .png-скриншоты вместо .pdf - свои особенности слива):
Как выбрать DLP-систему в 2026 году
Разбираем, как меняются критерии выбора DLP-систем и что теперь важно бизнесу.
