В предыдущей заметке отмечались варианты использования ATT&CK для центров мониторинга. Но не стоит недооценивать ее значимость для целей планирования и развития корпоративных средств защиты.
Совокупность мероприятий по обеспечению информационной безопасности должна быть адекватна актуальной модели нарушителя, но вечный вопрос CISO о том, сколько безопасности достаточно по-прежнему актуален, - наряду с недооценкой, возможны и перегибы. Где же искать эту золотую середину?
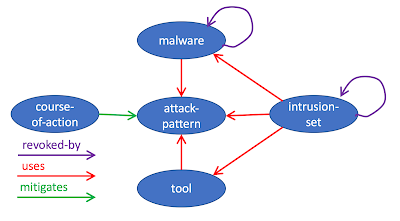
Если допустить, что совокупность техник и тактик MITRE является компиляцией современного ландшафта угроз (известного на данный момент, ну а защищаться от неизвестного - невозможно, и, как результат это приведет на необоснованным затратам на ИБ), то одним из возможных вариантов отстройки корпоративной СУИБ, является набор мероприятий по противостоянию угрозам из этой базы знаний. Благо, что вся база знаний доступна в машиночитаемом формате, что позволяет ее удобно анализировать. В конце этой заметки я привел таблички из Jupyter ноутбук, доступного здесь, в качестве примера такого анализа для Windows (сразу хочу попросить извинения у фанатов Python за, полагаю, не самый красивый код, ибо, будучи закоренелым Perl-истом, так до сих пор и не привык к многим особенностям этого языка, хотя, безусловно, вариант писать на С++ меня привлекает значительно меньше). В табличке "APT actors uses Techniques" я привел список техник, упорядоченный по количеству группировок (intrusion-set) их используемых. Также приведены связанные с техниками варианты ВПО (malware), и другие инструменты, не являющиеся в явном виде ВПО (tool). Наибольший интерес для планирования и развития корпоративных технологий защиты представляет колонка необходимой телеметрии (data_sources). Вообще, про структуру ATT&CK написано здесь, в схеме 2 на стр. 12, однако, формат машиночитаемого (далее MR) json-а я бы предпочел изобразить так (см табличку Number of objects of different type).
Из таблички "APT actors uses Techniques" можно сделать предположение какие техники наиболее часто используются публично известными на сейчас группировками и, с известной степенью допущения, в соответствии с ней можно планировать приоритетность и этапность развития корпоративных систем обнаружения и предотвращения компьютерных атак.
Весьма немаловажным является последний столбик - data_sources, показывающий, фактически, какие логи необходимы для обнаружения использования соответствующей техники.
В последний табличке Приложений - Telemetry required for Techniques - отражено какое количество техник можно продектить имея ту или иную телеметрию. Из нее можно сделать немаловажное наблюдение, которого мы немного коснемся в следующей заметке.
Подведу краткий вывод: MITRE ATT&CK может вполне служить некоторым наукообразным обоснованием необходимости внедрения в корпорации соответствующих систем безопасности (== поставляющих соответствующую телеметрию), а также основой для формирования этапов и приоритетов для таких проектов.
Приложения
Совокупность мероприятий по обеспечению информационной безопасности должна быть адекватна актуальной модели нарушителя, но вечный вопрос CISO о том, сколько безопасности достаточно по-прежнему актуален, - наряду с недооценкой, возможны и перегибы. Где же искать эту золотую середину?
Если допустить, что совокупность техник и тактик MITRE является компиляцией современного ландшафта угроз (известного на данный момент, ну а защищаться от неизвестного - невозможно, и, как результат это приведет на необоснованным затратам на ИБ), то одним из возможных вариантов отстройки корпоративной СУИБ, является набор мероприятий по противостоянию угрозам из этой базы знаний. Благо, что вся база знаний доступна в машиночитаемом формате, что позволяет ее удобно анализировать. В конце этой заметки я привел таблички из Jupyter ноутбук, доступного здесь, в качестве примера такого анализа для Windows (сразу хочу попросить извинения у фанатов Python за, полагаю, не самый красивый код, ибо, будучи закоренелым Perl-истом, так до сих пор и не привык к многим особенностям этого языка, хотя, безусловно, вариант писать на С++ меня привлекает значительно меньше). В табличке "APT actors uses Techniques" я привел список техник, упорядоченный по количеству группировок (intrusion-set) их используемых. Также приведены связанные с техниками варианты ВПО (malware), и другие инструменты, не являющиеся в явном виде ВПО (tool). Наибольший интерес для планирования и развития корпоративных технологий защиты представляет колонка необходимой телеметрии (data_sources). Вообще, про структуру ATT&CK написано здесь, в схеме 2 на стр. 12, однако, формат машиночитаемого (далее MR) json-а я бы предпочел изобразить так (см табличку Number of objects of different type).
Весьма немаловажным является последний столбик - data_sources, показывающий, фактически, какие логи необходимы для обнаружения использования соответствующей техники.
В последний табличке Приложений - Telemetry required for Techniques - отражено какое количество техник можно продектить имея ту или иную телеметрию. Из нее можно сделать немаловажное наблюдение, которого мы немного коснемся в следующей заметке.
Подведу краткий вывод: MITRE ATT&CK может вполне служить некоторым наукообразным обоснованием необходимости внедрения в корпорации соответствующих систем безопасности (== поставляющих соответствующую телеметрию), а также основой для формирования этапов и приоритетов для таких проектов.
Приложения
Number of objects of different type
| Object | Cnt |
|---|---|
| attack-pattern | 223 |
| relationship:course-of-action->mitigates->attack-pattern | 222 |
| relationship:intrusion-set->uses->attack-pattern | 884 |
| relationship:intrusion-set->uses->malware | 199 |
| relationship:intrusion-set->uses->tool | 144 |
| relationship:malware->uses->attack-pattern | 2065 |
| relationship:tool->uses->attack-pattern | 208 |
| relationship:intrusion-set->revoked-by->intrusion-set | 2 |
| relationship:malware->revoked-by->malware | 1 |
| course-of-action | 222 |
| identity | 1 |
| intrusion-set | 80 |
| malware | 237 |
| tool | 47 |
| x-mitre-matrix | 1 |
| x-mitre-tactic | 11 |
| marking-definition | 1 |
APT actors uses Techniques
| technique | intrusion-set | malware | tool | data_sources |
|---|---|---|---|---|
| T1064: Scripting | 31 | 19 | 3 | Process monitoring File monitoring Process command-line parameters |
| T1086: PowerShell | 28 | 15 | 3 | Windows Registry File monitoring Process monitoring Process command-line parameters |
| T1003: Credential Dumping | 27 | 21 | 13 | API monitoring Process monitoring PowerShell logs Process command-line parameters |
| T1204: User Execution | 26 | 1 | 0 | Anti-virus Process command-line parameters Process monitoring |
| T1027: Obfuscated Files or Information | 24 | 62 | 2 | Network protocol analysis Process use of network File monitoring Malware reverse engineering Binary file metadata Process command-line parameters Environment variable Process monitoring Windows event logs Network intrusion detection system Email gateway SSL/TLS inspection |
| T1059: Command-Line Interface | 23 | 85 | 4 | Process monitoring Process command-line parameters |
| T1060: Registry Run Keys / Startup Folder | 23 | 68 | 2 | Windows Registry File monitoring |
| T1105: Remote File Copy | 23 | 97 | 6 | File monitoring Packet capture Process use of network Netflow/Enclave netflow Network protocol analysis Process monitoring |
| T1193: Spearphishing Attachment | 23 | 0 | 0 | File monitoring Packet capture Network intrusion detection system Detonation chamber Email gateway Mail server |
| T1071: Standard Application Layer Protocol | 21 | 104 | 2 | Packet capture Netflow/Enclave netflow Process use of network Malware reverse engineering Process monitoring |
| T1107: File Deletion | 18 | 64 | 2 | File monitoring Process command-line parameters Binary file metadata |
| T1078: Valid Accounts | 18 | 4 | 1 | Authentication logs Process monitoring |
| T1053: Scheduled Task | 17 | 22 | 4 | File monitoring Process monitoring Process command-line parameters Windows event logs |
| T1002: Data Compressed | 15 | 14 | 1 | Binary file metadata File monitoring Process command-line parameters Process monitoring |
| T1083: File and Directory Discovery | 15 | 81 | 3 | File monitoring Process monitoring Process command-line parameters |
| T1082: System Information Discovery | 15 | 99 | 4 | Process monitoring Process command-line parameters |
| T1005: Data from Local System | 14 | 20 | 4 | File monitoring Process monitoring Process command-line parameters |
| T1057: Process Discovery | 14 | 66 | 4 | Process monitoring Process command-line parameters |
| T1016: System Network Configuration Discovery | 13 | 57 | 7 | Process monitoring Process command-line parameters |
| T1074: Data Staged | 12 | 22 | 0 | File monitoring Process monitoring Process command-line parameters |
| T1189: Drive-by Compromise | 12 | 2 | 0 | Packet capture Network device logs Process use of network Web proxy Network intrusion detection system SSL/TLS inspection |
| T1076: Remote Desktop Protocol | 12 | 1 | 4 | Authentication logs Netflow/Enclave netflow Process monitoring |
| T1018: Remote System Discovery | 12 | 10 | 3 | Network protocol analysis Process monitoring Process use of network Process command-line parameters |
| T1192: Spearphishing Link | 12 | 0 | 0 | Packet capture Web proxy Email gateway Detonation chamber SSL/TLS inspection DNS records Mail server |
| T1033: System Owner/User Discovery | 12 | 45 | 2 | File monitoring Process monitoring Process command-line parameters |
| T1056: Input Capture | 11 | 44 | 4 | Windows Registry Kernel drivers Process monitoring API monitoring |
| T1036: Masquerading | 11 | 33 | 1 | File monitoring Process monitoring Binary file metadata |
| T1087: Account Discovery | 10 | 19 | 4 | API monitoring Process monitoring Process command-line parameters |
| T1140: Deobfuscate/Decode Files or Information | 10 | 20 | 1 | File monitoring Process monitoring Process command-line parameters |
| T1116: Code Signing | 9 | 11 | 2 | Binary file metadata |
| T1043: Commonly Used Port | 9 | 40 | 2 | Packet capture Netflow/Enclave netflow Process use of network Process monitoring |
| T1203: Exploitation for Client Execution | 9 | 2 | 0 | Anti-virus System calls Process monitoring |
| T1055: Process Injection | 9 | 28 | 4 | API monitoring Windows Registry File monitoring DLL monitoring Process monitoring Named Pipes |
| T1102: Web Service | 9 | 20 | 0 | Host network interface Netflow/Enclave netflow Network protocol analysis Packet capture SSL/TLS inspection |
| T1047: Windows Management Instrumentation | 9 | 12 | 3 | Authentication logs Netflow/Enclave netflow Process monitoring Process command-line parameters |
| T1022: Data Encrypted | 8 | 18 | 0 | File monitoring Process monitoring Process command-line parameters Binary file metadata |
| T1050: New Service | 8 | 36 | 1 | Windows Registry Process monitoring Process command-line parameters Windows event logs |
| T1113: Screen Capture | 8 | 50 | 3 | API monitoring Process monitoring File monitoring |
| T1032: Standard Cryptographic Protocol | 8 | 37 | 3 | Packet capture Netflow/Enclave netflow Malware reverse engineering Process use of network Process monitoring SSL/TLS inspection |
| T1049: System Network Connections Discovery | 8 | 13 | 4 | Process monitoring Process command-line parameters |
| T1077: Windows Admin Shares | 8 | 6 | 3 | Process use of network Authentication logs Process monitoring Process command-line parameters |
| T1068: Exploitation for Privilege Escalation | 7 | 4 | 1 | Windows Error Reporting Process monitoring Application logs |
| T1112: Modify Registry | 7 | 26 | 2 | Windows Registry File monitoring Process monitoring Process command-line parameters Windows event logs |
| T1046: Network Service Scanning | 7 | 5 | 3 | Netflow/Enclave netflow Network protocol analysis Packet capture Process command-line parameters Process use of network |
| T1045: Software Packing | 7 | 11 | 0 | Binary file metadata |
| T1119: Automated Collection | 6 | 11 | 0 | File monitoring Data loss prevention Process command-line parameters |
| T1110: Brute Force | 6 | 2 | 0 | Authentication logs |
| T1088: Bypass User Account Control | 6 | 11 | 4 | System calls Process monitoring Authentication logs Process command-line parameters |
| T1073: DLL Side-Loading | 6 | 11 | 0 | Process use of network Process monitoring Loaded DLLs |
| T1089: Disabling Security Tools | 6 | 20 | 1 | API monitoring File monitoring Services Windows Registry Process command-line parameters Anti-virus |
| T1114: Email Collection | 6 | 6 | 1 | Authentication logs File monitoring Process monitoring Process use of network |
| T1133: External Remote Services | 6 | 0 | 0 | Authentication logs |
| T1070: Indicator Removal on Host | 6 | 12 | 1 | File monitoring Process monitoring Process command-line parameters API monitoring Windows event logs |
| T1012: Query Registry | 6 | 27 | 2 | Windows Registry Process monitoring Process command-line parameters |
| T1108: Redundant Access | 6 | 1 | 0 | Process monitoring Process use of network Packet capture Network protocol analysis File monitoring Authentication logs Binary file metadata |
| T1009: Binary Padding | 5 | 8 | 0 | Binary file metadata File monitoring Malware reverse engineering |
| T1090: Connection Proxy | 5 | 15 | 4 | Process use of network Process monitoring Netflow/Enclave netflow Packet capture |
| T1173: Dynamic Data Exchange | 5 | 2 | 0 | API monitoring DLL monitoring Process monitoring Windows Registry Windows event logs |
| T1041: Exfiltration Over Command and Control Channel | 5 | 11 | 1 | User interface Process monitoring |
| T1066: Indicator Removal from Tools | 5 | 2 | 2 | Process use of network Process monitoring Process command-line parameters Anti-virus Binary file metadata |
| T1069: Permission Groups Discovery | 5 | 9 | 2 | API monitoring Process monitoring Process command-line parameters |
| T1117: Regsvr32 | 5 | 3 | 1 | Loaded DLLs Process monitoring Windows Registry Process command-line parameters |
| T1085: Rundll32 | 5 | 24 | 1 | File monitoring Process monitoring Process command-line parameters Binary file metadata |
| T1023: Shortcut Modification | 5 | 15 | 0 | File monitoring Process monitoring Process command-line parameters |
| T1007: System Service Discovery | 5 | 18 | 2 | Process monitoring Process command-line parameters |
| T1065: Uncommonly Used Port | 5 | 11 | 0 | Netflow/Enclave netflow Process use of network Process monitoring |
| T1015: Accessibility Features | 4 | 0 | 0 | Windows Registry File monitoring Process monitoring |
| T1094: Custom Command and Control Protocol | 4 | 26 | 1 | Packet capture Netflow/Enclave netflow Process use of network Process monitoring Host network interface Network intrusion detection system Network protocol analysis |
| T1132: Data Encoding | 4 | 22 | 0 | Packet capture Process use of network Process monitoring Network protocol analysis |
| T1048: Exfiltration Over Alternative Protocol | 4 | 5 | 2 | User interface Process monitoring Process use of network Packet capture Netflow/Enclave netflow Network protocol analysis |
| T1100: Web Shell | 4 | 4 | 0 | Anti-virus Authentication logs File monitoring Netflow/Enclave netflow Process monitoring |
| T1098: Account Manipulation | 3 | 2 | 1 | Authentication logs API monitoring Windows event logs Packet capture |
| T1223: Compiled HTML File | 3 | 0 | 0 | File monitoring Process monitoring Process command-line parameters |
| T1136: Create Account | 3 | 5 | 2 | Process monitoring Process command-line parameters Authentication logs Windows event logs |
| T1039: Data from Network Shared Drive | 3 | 2 | 0 | File monitoring Process monitoring Process command-line parameters |
| T1075: Pass the Hash | 3 | 0 | 3 | Authentication logs |
| T1120: Peripheral Device Discovery | 3 | 9 | 0 | |
| T1093: Process Hollowing | 3 | 7 | 1 | Process monitoring API monitoring |
| T1219: Remote Access Tools | 3 | 1 | 0 | Network intrusion detection system Network protocol analysis Process use of network Process monitoring |
| T1021: Remote Services | 3 | 1 | 1 | Authentication logs |
| T1063: Security Software Discovery | 3 | 28 | 2 | File monitoring Process monitoring Process command-line parameters |
| T1124: System Time Discovery | 3 | 10 | 1 | Process monitoring Process command-line parameters API monitoring |
| T1099: Timestomp | 3 | 14 | 1 | File monitoring Process monitoring Process command-line parameters |
| T1134: Access Token Manipulation | 2 | 5 | 3 | API monitoring Access tokens Process monitoring Process command-line parameters |
| T1067: Bootkit | 2 | 3 | 0 | API monitoring MBR VBR |
| T1191: CMSTP | 2 | 0 | 0 | Process monitoring Process command-line parameters Process use of network Windows event logs |
| T1024: Custom Cryptographic Protocol | 2 | 32 | 0 | Packet capture Netflow/Enclave netflow Process use of network Malware reverse engineering Process monitoring |
| T1038: DLL Search Order Hijacking | 2 | 8 | 1 | File monitoring DLL monitoring Process monitoring Process command-line parameters |
| T1001: Data Obfuscation | 2 | 15 | 0 | Packet capture Process use of network Process monitoring Network protocol analysis |
| T1213: Data from Information Repositories | 2 | 0 | 1 | Application logs Authentication logs Data loss prevention Third-party application logs |
| T1025: Data from Removable Media | 2 | 9 | 0 | File monitoring Process monitoring Process command-line parameters |
| T1106: Execution through API | 2 | 10 | 1 | API monitoring Process monitoring |
| T1008: Fallback Channels | 2 | 17 | 0 | Malware reverse engineering Netflow/Enclave netflow Packet capture Process monitoring Process use of network |
| T1187: Forced Authentication | 2 | 0 | 0 | File monitoring Network protocol analysis Network device logs Process use of network |
| T1158: Hidden Files and Directories | 2 | 5 | 0 | File monitoring Process monitoring Process command-line parameters |
| T1031: Modify Existing Service | 2 | 5 | 1 | Windows Registry File monitoring Process monitoring Process command-line parameters |
| T1170: Mshta | 2 | 2 | 1 | Process monitoring Process command-line parameters |
| T1135: Network Share Discovery | 2 | 4 | 4 | Process monitoring Process command-line parameters Network protocol analysis Process use of network |
| T1097: Pass the Ticket | 2 | 1 | 1 | Authentication logs |
| T1091: Replication Through Removable Media | 2 | 8 | 0 | File monitoring Data loss prevention |
| T1035: Service Execution | 2 | 7 | 7 | Windows Registry Process monitoring Process command-line parameters |
| T1194: Spearphishing via Service | 2 | 0 | 0 | SSL/TLS inspection Anti-virus Web proxy |
| T1095: Standard Non-Application Layer Protocol | 2 | 13 | 0 | Host network interface Netflow/Enclave netflow Network intrusion detection system Network protocol analysis Packet capture Process use of network |
| T1221: Template Injection | 2 | 0 | 0 | Anti-virus Email gateway Network intrusion detection system Web logs |
| T1199: Trusted Relationship | 2 | 0 | 0 | Application logs Authentication logs Third-party application logs |
| T1084: Windows Management Instrumentation Event Subscription | 2 | 3 | 0 | WMI Objects |
| T1182: AppCert DLLs | 1 | 1 | 0 | Loaded DLLs Process monitoring Windows Registry |
| T1017: Application Deployment Software | 1 | 0 | 0 | File monitoring Process use of network Process monitoring |
| T1138: Application Shimming | 1 | 0 | 0 | Loaded DLLs System calls Windows Registry Process monitoring Process command-line parameters |
| T1010: Application Window Discovery | 1 | 8 | 0 | API monitoring Process monitoring Process command-line parameters |
| T1123: Audio Capture | 1 | 9 | 2 | API monitoring Process monitoring File monitoring |
| T1020: Automated Exfiltration | 1 | 4 | 0 | File monitoring Process monitoring Process use of network |
| T1197: BITS Jobs | 1 | 1 | 1 | API monitoring Packet capture Windows event logs |
| T1092: Communication Through Removable Media | 1 | 2 | 0 | File monitoring Data loss prevention |
| T1109: Component Firmware | 1 | 0 | 0 | Disk forensics API monitoring Process monitoring Component firmware |
| T1122: Component Object Model Hijacking | 1 | 5 | 0 | Windows Registry DLL monitoring Loaded DLLs |
| T1081: Credentials in Files | 1 | 7 | 2 | File monitoring Process command-line parameters |
| T1030: Data Transfer Size Limits | 1 | 4 | 0 | Packet capture Netflow/Enclave netflow Process use of network Process monitoring |
| T1172: Domain Fronting | 1 | 0 | 1 | SSL/TLS inspection Packet capture |
| T1190: Exploit Public-Facing Application | 1 | 0 | 2 | Packet capture Web logs Web application firewall logs Application logs |
| T1211: Exploitation for Defense Evasion | 1 | 0 | 0 | Windows Error Reporting Process monitoring File monitoring |
| T1210: Exploitation of Remote Services | 1 | 1 | 0 | Windows Error Reporting Process monitoring File monitoring |
| T1061: Graphical User Interface | 1 | 0 | 0 | File monitoring Process monitoring Process command-line parameters Binary file metadata |
| T1179: Hooking | 1 | 1 | 0 | API monitoring Binary file metadata DLL monitoring Loaded DLLs Process monitoring Windows event logs |
| T1037: Logon Scripts | 1 | 1 | 0 | File monitoring Process monitoring |
| T1104: Multi-Stage Channels | 1 | 3 | 0 | Netflow/Enclave netflow Network device logs Network protocol analysis Packet capture Process use of network |
| T1188: Multi-hop Proxy | 1 | 3 | 1 | Network protocol analysis Netflow/Enclave netflow |
| T1026: Multiband Communication | 1 | 1 | 1 | Packet capture Netflow/Enclave netflow Process use of network Malware reverse engineering Process monitoring |
| T1126: Network Share Connection Removal | 1 | 0 | 1 | Process monitoring Process command-line parameters Packet capture Authentication logs |
| T1040: Network Sniffing | 1 | 1 | 1 | Network device logs Host network interface Netflow/Enclave netflow Process monitoring |
| T1137: Office Application Startup | 1 | 0 | 0 | Process monitoring Process command-line parameters Windows Registry File monitoring |
| T1201: Password Policy Discovery | 1 | 1 | 1 | Process command-line parameters Process monitoring |
| T1014: Rootkit | 1 | 6 | 0 | BIOS MBR System calls |
| T1216: Signed Script Proxy Execution | 1 | 0 | 0 | Process monitoring Process command-line parameters |
| T1195: Supply Chain Compromise | 1 | 2 | 0 | Web proxy File monitoring |
| T1080: Taint Shared Content | 1 | 2 | 0 | File monitoring Process monitoring |
| T1072: Third-party Software | 1 | 1 | 0 | File monitoring Third-party application logs Windows Registry Process monitoring Process use of network Binary file metadata |
| T1125: Video Capture | 1 | 7 | 2 | Process monitoring File monitoring API monitoring |
| T1028: Windows Remote Management | 1 | 0 | 1 | File monitoring Authentication logs Netflow/Enclave netflow Process monitoring Process command-line parameters |
| T1004: Winlogon Helper DLL | 1 | 2 | 0 | Windows Registry File monitoring Process monitoring |
| T1220: XSL Script Processing | 1 | 0 | 0 | Process monitoring Process command-line parameters Process use of network DLL monitoring |
| T1103: AppInit DLLs | 0 | 2 | 0 | Loaded DLLs Process monitoring Windows Registry |
| T1131: Authentication Package | 0 | 1 | 0 | DLL monitoring Windows Registry Loaded DLLs |
| T1217: Browser Bookmark Discovery | 0 | 2 | 0 | API monitoring File monitoring Process command-line parameters Process monitoring |
| T1176: Browser Extensions | 0 | 0 | 0 | Network protocol analysis Packet capture System calls Process use of network Process monitoring Browser extensions |
| T1042: Change Default File Association | 0 | 0 | 0 | Windows Registry Process monitoring Process command-line parameters |
| T1115: Clipboard Data | 0 | 9 | 1 | API monitoring |
| T1196: Control Panel Items | 0 | 1 | 0 | API monitoring Binary file metadata DLL monitoring Windows Registry Windows event logs Process command-line parameters Process monitoring |
| T1214: Credentials in Registry | 0 | 0 | 2 | Windows Registry Process command-line parameters Process monitoring |
| T1207: DCShadow | 0 | 0 | 1 | API monitoring Authentication logs Network protocol analysis Packet capture |
| T1175: Distributed Component Object Model | 0 | 1 | 1 | API monitoring Authentication logs DLL monitoring Packet capture Process monitoring Windows Registry Windows event logs |
| T1129: Execution through Module Load | 0 | 2 | 0 | API monitoring DLL monitoring File monitoring Process monitoring |
| T1011: Exfiltration Over Other Network Medium | 0 | 1 | 0 | User interface Process monitoring |
| T1052: Exfiltration Over Physical Medium | 0 | 4 | 0 | Data loss prevention File monitoring |
| T1212: Exploitation for Credential Access | 0 | 0 | 0 | Authentication logs Windows Error Reporting Process monitoring |
| T1181: Extra Window Memory Injection | 0 | 1 | 0 | API monitoring Process monitoring |
| T1222: File Permissions Modification | 0 | 1 | 0 | File monitoring Process monitoring Process command-line parameters Windows event logs |
| T1006: File System Logical Offsets | 0 | 0 | 0 | API monitoring |
| T1044: File System Permissions Weakness | 0 | 1 | 0 | File monitoring Services Process command-line parameters |
| T1200: Hardware Additions | 0 | 0 | 0 | Asset management Data loss prevention |
| T1062: Hypervisor | 0 | 0 | 0 | System calls |
| T1183: Image File Execution Options Injection | 0 | 0 | 0 | Process monitoring Windows Registry Windows event logs |
| T1054: Indicator Blocking | 0 | 0 | 0 | Sensor health and status Process command-line parameters Process monitoring |
| T1202: Indirect Command Execution | 0 | 0 | 1 | Process monitoring Process command-line parameters Windows event logs |
| T1130: Install Root Certificate | 0 | 2 | 1 | SSL/TLS inspection Digital certificate logs |
| T1118: InstallUtil | 0 | 0 | 0 | Process monitoring Process command-line parameters |
| T1208: Kerberoasting | 0 | 0 | 1 | Windows event logs |
| T1171: LLMNR/NBT-NS Poisoning | 0 | 0 | 2 | Windows Registry Packet capture Netflow/Enclave netflow |
| T1177: LSASS Driver | 0 | 2 | 0 | API monitoring DLL monitoring File monitoring Kernel drivers Loaded DLLs Process monitoring |
| T1185: Man in the Browser | 0 | 1 | 1 | Authentication logs Packet capture Process monitoring API monitoring |
| T1079: Multilayer Encryption | 0 | 2 | 2 | Packet capture Process use of network Malware reverse engineering Process monitoring |
| T1096: NTFS File Attributes | 0 | 5 | 0 | File monitoring Kernel drivers API monitoring Process command-line parameters |
| T1128: Netsh Helper DLL | 0 | 0 | 1 | DLL monitoring Windows Registry Process monitoring |
| T1174: Password Filter DLL | 0 | 1 | 0 | DLL monitoring Process monitoring Windows Registry |
| T1034: Path Interception | 0 | 0 | 1 | File monitoring Process monitoring |
| T1013: Port Monitors | 0 | 0 | 0 | File monitoring API monitoring DLL monitoring Windows Registry Process monitoring |
| T1145: Private Keys | 0 | 0 | 1 | File monitoring |
| T1186: Process Doppelg?nging | 0 | 1 | 0 | API monitoring Process monitoring |
| T1121: Regsvcs/Regasm | 0 | 0 | 0 | Process monitoring Process command-line parameters |
| T1178: SID-History Injection | 0 | 0 | 1 | API monitoring Authentication logs Windows event logs |
| T1198: SIP and Trust Provider Hijacking | 0 | 0 | 0 | API monitoring Application logs DLL monitoring Loaded DLLs Process monitoring Windows Registry Windows event logs |
| T1029: Scheduled Transfer | 0 | 5 | 1 | Netflow/Enclave netflow Process use of network Process monitoring |
| T1180: Screensaver | 0 | 1 | 0 | Process monitoring Process command-line parameters Windows Registry File monitoring |
| T1101: Security Support Provider | 0 | 0 | 2 | DLL monitoring Windows Registry Loaded DLLs |
| T1058: Service Registry Permissions Weakness | 0 | 0 | 0 | Process command-line parameters Services Windows Registry |
| T1051: Shared Webroot | 0 | 0 | 0 | File monitoring Process monitoring |
| T1218: Signed Binary Proxy Execution | 0 | 0 | 0 | Process monitoring Process command-line parameters |
| T1019: System Firmware | 0 | 2 | 0 | API monitoring BIOS EFI |
| T1209: Time Providers | 0 | 0 | 0 | API monitoring Binary file metadata DLL monitoring File monitoring Loaded DLLs Process monitoring |
| T1127: Trusted Developer Utilities | 0 | 1 | 0 | Process monitoring |
| T1111: Two-Factor Authentication Interception | 0 | 1 | 0 | API monitoring Process monitoring Kernel drivers |
Telemetry required for Techniques
| data_sources | attack-pattern |
|---|---|
| Process monitoring | 136 |
| Process command-line parameters | 76 |
| File monitoring | 68 |
| API monitoring | 39 |
| Process use of network | 36 |
| Windows Registry | 34 |
| Packet capture | 32 |
| Authentication logs | 24 |
| Netflow/Enclave netflow | 24 |
| Windows event logs | 19 |
| Network protocol analysis | 18 |
| DLL monitoring | 17 |
| Binary file metadata | 16 |
| Loaded DLLs | 12 |
| Malware reverse engineering | 8 |
| SSL/TLS inspection | 8 |
| Network intrusion detection system | 7 |
| Anti-virus | 7 |
| System calls | 6 |
| Data loss prevention | 6 |
| Application logs | 5 |
| Host network interface | 4 |
| Network device logs | 4 |
| Web proxy | 4 |
| Windows Error Reporting | 4 |
| Kernel drivers | 4 |
| Email gateway | 4 |
| Third-party application logs | 3 |
| Services | 3 |
| User interface | 3 |
| MBR | 2 |
| Web logs | 2 |
| BIOS | 2 |
| Detonation chamber | 2 |
| Mail server | 2 |
| Access tokens | 1 |
| VBR | 1 |
| Browser extensions | 1 |
| Disk forensics | 1 |
| Component firmware | 1 |
| PowerShell logs | 1 |
| Web application firewall logs | 1 |
| Asset management | 1 |
| Sensor health and status | 1 |
| Digital certificate logs | 1 |
| Environment variable | 1 |
| Named Pipes | 1 |
| DNS records | 1 |
| EFI | 1 |
| WMI Objects | 1 |