Adobe Experience Manager is content management system that is based on Apache Sling – a framework for RESTful web-applications based on an extensible content tree. Apache Sling in its turn is basically a REST API for Apache Jackrabbit, which is an implementation of Content Repository API for Java (JCR). The main principle of JCR is that everything is a resource. It means that any object in JCR repository can be retrieved in multiple ways depending on requested selector. E.g. if you make a request to /index.html you will get an HTML page, but if you replace .html with a .json selector you can get metadata of this resource:
{
"jcr:primaryType":"cq:Page",
"jcr:createdBy":"transport-user",
"jcr:created":"Mon Jun 13 2018 22:09:46 GMT+0000"
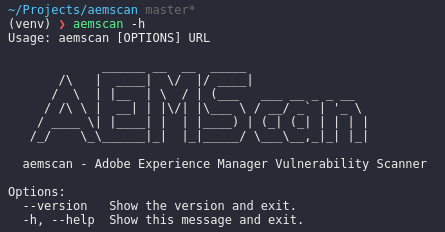
}AEM installations typically have lots of hidden gems (even password hashes) if selectors are improperly configured. aemscan helps to discover such weaknesses and much more:
- Default credentials bruteforce
- Info leak via default error page
- WebDav support check (WebDav OSGI XXE CVE-2015-1833)
- Version detection
- Useful paths scanner
You can grab the source code from GitHub: https://github.com/Raz0r/aemscan. Pull requests are welcome!
The post Adobe Experience Manager Vulnerability Scanner first appeared on Raz0r.name.